It is now easier to interfere with surveillance footage due to the increased sophistication of artificial intelligence tools.
Video manipulators are now able to edit videos in the manner that once cost Hollywood a budget and a staff of visual effects artists.
Therefore, should you be involved with security systems, then it is necessary that you understand why and how to protect surveillance footage against AI-based interference.
主要收获
- AI tampering is becoming more advanced
- Human eyes cannot be totally relied on to detect tampering
- AI has to be used to fight AI-generated tampering proactively
What is Surveillance Footage?
Just by looking at ‘surveillance’ and ‘footage’ separately, you probably have a rough idea of what surveillance footage means, but if you don’t, that is not a problem.
Surveillance footage is a video captured by security cameras. It is used for monitoring, recording, and reviewing activity in a specific location.
You can call it the digital eye of a property that shows a chronological record of reality.
Surveillance footage may come from a variety of sources, including:
- CCTV systems
- Office and warehouse monitoring cameras
- Retail store cameras
- Government security systems
- Smart home security cameras
This footage is used for many reasons, such as preventing crimes, investigating incidents, providing evidence in legal cases, and monitoring activities in real time.
Due to the use of these footages, surveillance security depends on trust. Therefore, once anything is captured on a security camera, it is assumed that whatever is on the security camera has actually occurred.
So, if a surveillance video is not reliable, then what is the use of the entire system? Now that’s where artificial intelligence tampering comes in.
Why AI Tampering is a Growing Threat
AI tampering is the deliberate and unauthorized activity of altering artificial intelligence systems with the aim of getting it to provide inaccurate, biased, or malicious outcomes.
It involves an attempt at interfering with AI training data, algorithms, or models in order to undermine the integrity and reliability of artificial intelligence.
So why is AI tampering a growing threat? To be honest, the same artificial intelligence that has given us many innovations has also given us tools to manipulate surveillance footage.
In the past, editing surveillance footage actually required you to have certain skills and software. It took a lot of time and expertise to manipulate a video. But now, there are dedicated AI tools that could manipulate a video at the touch of a button.
These tools can swap faces, alter timestamps, or remove people from scenes. By tampering, you can create a false video sequence that looks completely real.
The thing with tampering is that it is not just a theoretical issue; you can see real-life cases of manipulated footage that have been used to create false narratives, frame innocent people, and shake the credibility of legitimate security systems.
With these manipulations being difficult to detect, the stakes around surveillance security and security video integrity couldn’t be higher.
For organizations that rely on security video integrity, AI tampering is a big problem. They could rake up millions in debt in lawsuits.
Common Methods of AI Video Tampering
So, how exactly does AI tampering work? The following are the methods of AI tampering:
Frame Manipulation Techniques
This is one of the most basic forms of manipulation. It involves inserting, deleting, or replacing individual frames in a video sequence.
This technique may sound simple, but when it is done, it is almost impossible to detect.
Artificial Intelligence algorithms can analyze the lighting, motion blur, grain, and compression artifacts of existing footage and match them when inserting altered frames.
You could:
- Remove a person from a scene
- Change facial expressions
- Swap faces (deepfake-style)
- Edit actions so they appear different
With this, it is almost like the event never happened or the person was never there. A totally fabricated moment gets inserted, and you get results that look like the footage was never touched.
If no automated footage verification is done, you may never notice the manipulation.
Synthetic Overlays on Footage
This form of manipulation is unsettling, and it is mostly done with deepfake and generative AI technology. With this, it is possible to overlay synthetic content directly onto real video.
That is putting fake elements into real footage.
With synthetic overlays, you can
- Swap a person’s face for another person’s
- Change a license plate
- Insert or remove an object from a scene
- Add a weapon in someone’s hand
- Place someone where they never were
These synthetic overlays are generated by AI models that have been trained on large amounts of video data.
They are conditioned to merge well with the original video through correspondence on lighting, skin color, shadows, and minor movements that one would never pick up without knowledge of what to look for.
Altered Timestamps and Logs
Ordinarily, timestamps and metadata logs should be the safety net when verifying surveillance footage because they tell you when the footage was recorded and whether it has been modified.
However, with the new AI tampering technologies, it has become difficult to figure out time stamps.
By changing timestamps, metadata, and logs, attackers can make tampered footage to look like it was recorded at a different time.
One can even conceal evidence and make files appear as if they have never been opened or edited, or forge a good chain of custody that is good on paper.
There is an actual need to ensure that video tampering detection goes beyond just looking at pixels; it should involve examining the entire data around the footage.
Without automated footage verification, these changes can go unnoticed.
Red Flags for Detecting Tampered Footage
It is vital to know what to look for when trying to detect tampered footage.
Sometimes, obvious red flags of tampered footage include:
- Inconsistent lighting or shadows
- Unnatural blurring around the edges of objects or people
- Slight flickering in certain frames
- Audios and lip movement that are not in sync with the video
- Timestamps that jump or repeat unexpectedly
- Metadata that doesn’t match the recorded time or location.
While these signs look like they are easy to spot, the most sophisticated AI tampering is not this obvious.
That is why relying on human review alone is no longer enough giving the advancement of artificial intelligence. You need to detect with technology on your side and fight AI with AI.
Using AI Tools to Protect Footage and How it Works
It probably sounds ironic, but the same AI functions that make tampering possible are the same tools you need to detect and protect surveillance footage. Artificial Intelligence tools are the best defenses against AI manipulation.
The following are artificial tools that you need to protect footage, and how they work:
深度伪造检测器
A deepfake detector is an AI model that is designed and trained to identify the signatures of an AI manipulated video content. This tool analyzes videos and looks for little inconsistencies in facial movement and weird pixel patterns.
It also highlights the characteristics that show that the footage was processed after recording or modified by AI. A deepfake detector can be used to find out the changes in faces, synthetic overlays, and AI-generated scenes.
Deepfake detectors compare the visual fingerprint of a video to what the real footage is expected to resemble.
Then it raises a red flag on anything that does not appear right, such as:
- Irregular eye reflections
- Abnormal facial symmetry
- Blending inconsistencies
- Neural rendering artifacts
Real-time AI Detector
You can use a real-time AI detector to analyze surveillance footage as it is being recorded or streamed, rather than after the fact. In that manner, it is easy to determine whether something is wrong before it is too late.
A real-time AI detector works with your existing camera setup and runs continuous checks.
Therefore, in case a person is attempting to alter the footage during the recording process by looping a different piece of footage, a real-time AI detector can be used to identify it and produce an alert before the event occurs.
High-security settings that require immediate detection when a breach occurs are strongly advised to have real-time detectors. It is like an antivirus system but for video streams.
For high-security environments, this capability is basically non-negotiable.
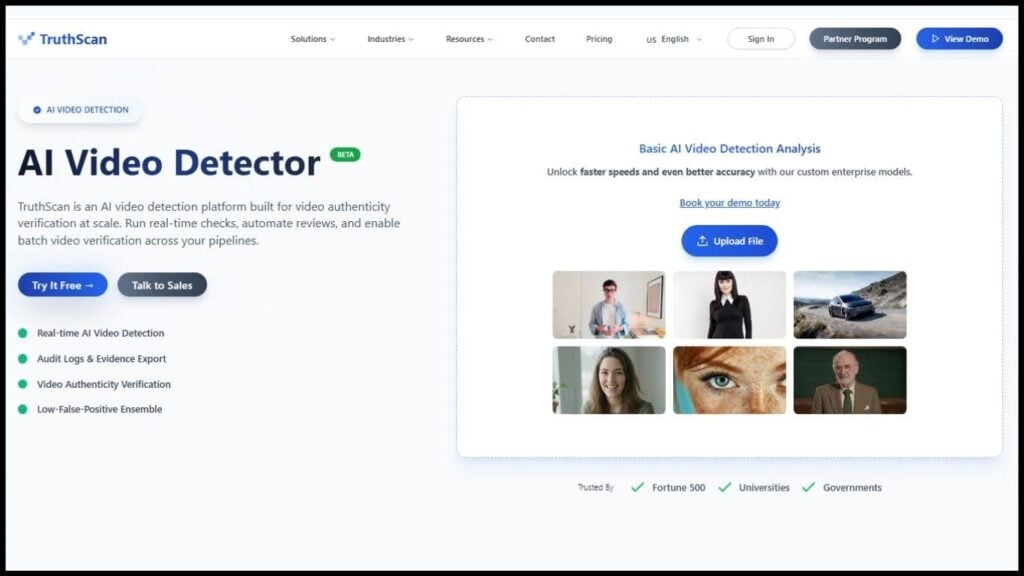
AI Video Detector
An artificial intelligence video detector is an all-encompassing way to check the originality of the footage. It is used to check the authenticity and integrity of a recorded video.
You can think of it as an audit system for your video.
The way this tool works is by looking at the full structure of a video. It goes beyond just analyzing the visuals; it checks out the encoding, compression, history, metadata, and file structure.
It detects:
- Common signs of tampering, like re-encoding
- If frames have been removed or added
- Whether the digital fingerprinting of the footage matches what it should be
- Motion inconsistencies
- Irregular lighting patterns
- Metadata changes
You can also combine the functions of this tool with the functions of a deepfake detector to get a complete picture of the footage.
This ensures that you can rely on the video 100% because the detection goes beyond facial edits.
The best way to create a strong AI footage protection system is by combining the functions of these tools. It is almost like a safe proof way to reduce the risk associated with AI tampering.
Integrating AI Protection Into Security Workflows
There are occasions when one may possess the correct knowledge, but they just need to know how to apply that knowledge.
Therefore, you may understand AI protection tools, but you still need to understand how to integrate them into your security processes.
This is how to implement AI protection in security processes:
- Begin at the Point of Capture: It is important to make sure that your cameras are capturing footage on a secure and tamper-evident storage system immediately they begin recording. You can use encrypted storage with access logs. This is a system that creates a cryptographic hash of each video from the moment it is recorded to the moment it is saved. That way, any alteration can be detected immediately.
- Have a System that Runs Continuously: There’s a need for automated footage verification tools that run continuously in the background. With that, you do not need to look through every hour of your footage manually. An automated system allows you to set alert thresholds so that you are alerted the moment something suspicious happens.
- Develop a Chain of Custody: Record all the activities that were done on your footage. Whenever your videos are accessed, transferred, or viewed, they must be logged. You can guarantee that nothing is tampered with between access points by creating a chain of custody with the help of an AI video detector.
- Develop a Team: To get your surveillance footage secure may be hectic, and this is why you would want to employ a team that operates 24 hours to record any tampering, should you be able to afford one.
It is not enough to just install detection software and move on. You need it to include it in your workflow. Your goal should be building automated footage verification into everyday operations and not just investigations alone.
So when you integrate AI protection into your workflow, it becomes harder to tamper with your footage.
Best Practices for Securing Surveillance Data
Apart from using AI Tools, there are basic steps that you must take for AI footage protection. These steps include:
- Encryption: By encrypting your recording data, you make it difficult for hackers to intercept and manipulate your surveillance footage.
- Limiting Access: This is to ensure that only authorised individuals are allowed to access footage, and every access is recorded and audited.
- Periodically Archive Footage: You must regularly store all your surveillance footage in more than one secure location. It should be like an off-site or cloud storage that is not available via your main network.
- Regular Firmware and Software updates: Your camera systems also need to be updated on a regular basis to make them less prone to manipulation. It also prevents hackers from tampering with your footage.
- Watermarking Your Video: Embedding a watermark, an invisible trace on your video, can act as an authentication of the video.
- Take Security Video Integrity Seriously: Taking steps to prevent tampering should be a regular thing. You need to regularly update your anti-tampering software and review your detection tools to ensure they are up to standard with evolving AI video tampering techniques.
How TruthScan Helps Enterprises Protect Video Evidence
Protecting video evidence requires you to use tools that you trust, and this is where 真相扫描 comes in. TruthScan is an AI detection platform with AI images, voice, and video detection capabilities.
It can identify manipulated, synthetic, and fraudulent images with enterprise-grade accuracy.
For businesses that deal with video evidence, 真相扫描 offers both an AI video detector and a deepfake detector. The AI Video Detector can assist in confirming videos and conducting real-time checks on a large scale.
Deepfakes produced by AI, manipulated video, and synthetic media are also detected by the deepfake detector.
Using both of these TruthScan tools, you are able to defend your organization against video fraud and manipulation that cannot be easily detected by the naked eye.
Talk to TruthScan About Securing Surveillance Footage Safely
Securing surveillance footage has gone beyond just reviewing video manually. People who rely on the naked eye or do not rely on anything at all are exposing themselves in ways they may not realize yet.
Nevertheless, the positive aspect is that it is quite possible to ensure that the footage is secured. It only requires the appropriate tools, including a deepfake detector or video detector.
TruthScan is ready to offer you these tools to help reduce vulnerability and make sure your footage remains trustworthy evidence.
Reach out to 真相扫描 today and find out how to secure your surveillance footage.
