Once you start running a business, you’ll come across fraudsters who want to take advantage of you, either by using fake IDs or other manipulated images.
With the rise of AI image generators like Nano Banana, it has become easier than ever for fraudsters to churn out fake images to test your defenses daily.
Due to this, you can’t rely solely on gut feeling to spot ID image fraud.
That’s why we’ve identified 8 indicators that can help you spot an image that has been manipulated, and also a great AI image detector to strengthen your fraud prevention strategy.
Principais conclusões
- AI swapping of faces onto legitimate ID templates often results in unnatural indicators like misaligned eyes, warped skin textures, or blurred halos around the head.
- Fraudsters struggle to replicate official government fonts perfectly, leading to detectable errors such as inconsistent text weights or letters sitting unevenly on the baseline.
- Digital manipulation frequently leaves behind hidden evidence in the form of software tags and metadata timestamps that do not match the document’s official issue date.
- Automated verification platforms are essential for enterprise security because human reviewers cannot keep pace with the massive volume of synthetic IDs created daily by AI tools.
Why Detecting Manipulated ID Images Matters
Manipulated ID images have become one of the easiest access points fraudsters have into your onboarding and account recovery flows.
As a result of this, real business impact shows up fast.
O FBI’s Internet Crime Complaint Center reported over 880,000 fraud complaints in 2023. Amongst these complaints, investment scams caused the heaviest blows.
Nunca mais se preocupe com fraudes de IA. TruthScan Pode lhe ajudar:
- Detectar IA gerada imagens, texto, voz e vídeo.
- Evitar grande fraude impulsionada por IA.
- Proteja seus mais sensível ativos da empresa.
Financial institutions and e-commerce companies are now finding themselves on the front lines as synthetic identities and manipulated documents bypass legacy verification systems.
In the meantime, your organization can’t afford to treat fake ID detection as an afterthought, as seen from a Trustpair Research report that revealed that 90% of U.S. companies experienced cyber fraud in 2024, and 47% of them reported losses exceeding $10M.
Therefore, detecting manipulated images matters because:
- Catching ID image fraud during onboarding is better than cleaning up chargebacks and investigations later.
- Know Your Customer (KYC) regulations demand strict AI image verification. Once this is enabled, you can avoid expensive fines.
- Strong AI image verification helps your team focus on the truly risky cases instead of chasing obvious noise.
- Manipulated ID detection supports consistent decision-making and clearer evidence trails when regulators and partners ask how you manage identity risk.
Indicator 1: Inconsistent Facial Features
This is the first indicator you have to look out for in fake IDs. Fraudsters frequently swap photos or use AI-generated images that can deceive you at first glance.
You have to look closely to see the subtle inconsistencies a human face won’t have, giving you an uncanny valley feeling.
The staggering spike in deepfake attacks tells you that fraudsters are betting heavily on facial manipulation because it works against weak verification systems.
Embora AI image generators are getting better at creating realistic human faces, your team and an AI image detector tool can zero in on these telltale signs:
- Eyes slightly misaligned
- Nose-to-mouth distance that looks compressed or stretched
- Skin tone mismatches
- Over-smoothed skin that resembles a beauty filter
- Unnatural eye reflections
- Ears that are partially missing or warped near the edges.
Having to carefully find these inconsistencies in thousands of IDs is unrealistic through your manual review.
However, our Detector de deepfake is an automated verification tool that scans and flags facial inconsistencies that human reviewers might overlook in record time.
So, don’t rely on guesswork and start running questionable media through TruthScan to confirm authenticity in seconds.
Indicator 2: Blurred or Altered Backgrounds
Every legitimate ID has a background that follows a strict style guide. For instance, government-issued documents use specific colors and patterns that remain consistent across millions of cards.
Sometimes, fraudsters focus all their energy on perfecting the face. This results in them leaving the background with dead giveaways that an observant person can catch.
Some red flags to look out for include:
- A blur that forms a halo around the hair or jawline.
- A sharp face, yet the immediate area next to the face turns soft too abruptly.
- The background inside the portrait photo looks studio-smooth, while the rest of the ID image shows normal grain.
Indicator 3: Suspicious Document Fonts
Fonts are one of the easiest parts to edit in an ID, and one of the hardest elements for fraudsters to replicate perfectly. Look no further than government agencies, which use highly specific fonts across their identity documents.
When a fraudster edits text fields on a stolen template, the fonts tend not to align like in the original.
Also, it has been noted that fraudsters commonly change high-value fields that chiefly contain name, date of birth, or expiry date. These fields are the core areas they use to swindle companies.
The edits they make often look fine at a glance, yet the letters sit slightly off the baseline. Other times, the text looks a touch bolder or thinner than the surrounding text.
Another glaring clue is when they use a sans-serif font in place of the Times New Roman font.
Indicator 4: Tampered Security Features
Government-issued IDs pack layers of security features that take years of research and millions of dollars to develop, just so these IDs are extremely difficult to replicate.
Fraudsters know this, and most don’t even try to recreate these features faithfully.
Instead, they rely on low-resolution scans and digital submissions where security scans are more lax.
Currently, many modern IDs have features such as UV ink and laser perforation to keep the document authentic. So, attempts to rework the surface can show up as distortion or broken patterns.
For your business, this indicator matters because although fraudsters can match fonts and layouts with reasonable accuracy, they can’t replicate embedded physical security features through digital tools.
That’s why they consistently fail.
Indicator 5: Metadata and File Anomalies
Digital media often has metadata that we can’t see just by looking at the image. The metadata gives scanning systems information about the file, such as how, when, and where an image was created.
Fraudsters rarely think about cleaning up this metadata trail. Which makes metadata analysis one of the best indicators in your fake ID detection process.
However, you must know that metadata can be altered. Nevertheless, treat it as a risk signal for review teams.
These are other file anomalies you’ll have to look out for:
| Anomaly Type | What it Reveals |
| Editing software tags | This shows what editing software, like Adobe Photoshop, has altered the image before submission |
| Mismatched timestamps | The ID issue date doesn’t align with the image creation date. This suggests post-production manipulation. |
| GPS data conflicts | The location data embedded in the file doesn’t match the applicant’s stated address. |
| Compression artifacts | An image that has gone through multiple rounds of saving and editing will degrade the image quality. |
| Format inconsistencies | This is when your system receives a document in an unusual format when it expects JPEG or PNG. |
Indicator 6: Odd Color or Lighting
Odd color and lighting in manipulated images show up when a fraudster pastes a new face onto a real ID or cleans up a photo with heavy editing.
Research on deepfake and manipulation detection consistently points to color and lighting discrepancies, such as
- Unnatural illumination gradients through the image
- Synthetic shadows, and
- Inconsistent reflections in the eyes and glasses.
Notwithstanding, genuine ID photos are captured under controlled studio conditions with standardized lighting setups.
This produces:
- Consistent color temperatures,
- Uniform shadow distribution, and
- Predictable skin tone rendering across the entire image.
The moment someone introduces elements from a different source, this consistency is lost.
A good AI image detector can detect these inconsistencies at scale during AI image verification, so your team doesn’t have to rely on guesswork.
Indicator 7: Duplicate or Reused ID Images
Fraudsters are practical creatures, and when they create a convincing ID, they squeeze every drop of value from it.
This means submitting the same image or similar variations of it across multiple platforms and accounts.
Fraud rings do this to move faster and keep trying until one attempt slips through their numerous accounts.
Jumio highlighted a stat (sourced from RSA Security) that 48% of fraud comes from accounts that are less than a day old.
This recycling habit creates a detection opportunity your business should actively exploit early to protect your downstream teams.
You can also watch for the following behavioral patterns that often accompany duplicate submissions:
- Multiple accounts using similar documents with nearly identical photo compositions.
- A single device or IP address that submits multiple verification requests in minutes.
- Fraudsters reusing the same photo while changing the name or address fields.
- The same ID image appears in different geographic locations within an unrealistic timeframe. This signals coordinated fraud activity that warrants immediate identity fraud alerts.
Meanwhile, every duplicate image your deepfake detector catches today prevents multiple fraud attempts tomorrow. Fraudsters banking on the assumption that your platform operates in isolation will be consistently exposed.
Indicator 8: Mismatched Personal Details
Fraudsters juggling multiple fake identities eventually trip over themselves due to minor details.
Every piece of personal information on the ID needs to align perfectly with external data sources, and this is where just a convincing image fails.
Por exemplo,
- A date of birth that makes the applicant 16, but pairs with a photo of someone clearly in their 30s.
- An address formatted in a style the issuing state never uses.
- An ID number that fails verification because the fraudster generated it randomly rather than following the issuing authority’s secret algorithmic structure.
Thus, you need a comprehensive fake ID detection process that uses personal detail verification and image analysis. A document might pass visual inspection while failing data validation, or vice versa.
Layering both approaches ensures that your identity fraud alerts fire from multiple angles. This will leave fraudsters with nowhere to hide.
How Enterprises Can Detect and Prevent ID Fraud
Your enterprise ID detection programs will be unreliable when reviews depend on good eyes and luck to detect fake IDs.
Right now, digital manipulation is the main process fraudsters use to overwhelm manual reviewers. Many of them are successfully scamming organizations, leading to financial losses yearly.
That’s why scalable AI verification systems matter for you, because you want consistent fake ID detection, reliable identity fraud alerts, and a workflow your team can rely on every day. This is how you do it:
AI Verification Tools
Modern AI image verification works best as a layered set of checks, from the onboarding process up to the full registration.
Hence, when you integrate an AI image detector into your workflow, it analyzes submitted documents across hundreds of data points simultaneously.
It then delivers its verdict in seconds that would take human reviewers hours to reach.
In an effort to strengthen identity verification, the National Institute of Standards and Technology (NIST) suggested digital identity guidance calls for analyzing submitted media.
These include indicators of any form of modification and using live capture plus document checks to reduce injected or manipulated copies.
All this can be effectively handled by AI verification tools. All you have to do is prioritize platforms that offer real-time analysis without sacrificing accuracy.
The tool must provide confidence scores alongside nuanced information to enable your team review and decide for borderline cases.
Embed Detection Workflows
Detection only pays off when it changes what happens next. Many teams still lean heavily on people to carry the load; in this scenario, fake IDs are bound to slip through.
Even with this, technology alone won’t protect your business without structured workflows that ensure every submission follows a consistent verification path.
Embedding manipulated ID detection into your operational processes creates repeatable checkpoints that leave no room for shortcuts.
Also include clear escalation criteria, where initial AI screening handles high-volume filtering while specialized review teams handle extreme cases.
Programas de treinamento de funcionários
Your employees remain your most adaptable line of defense. Undoubtedly, AI image verification tools process data at scale and with speed, yet trained employees bring contextual judgment that technology cannot replicate.
In fact, the Association of Certified Fraud Examiners stresses that these training programs should be mandatory in organizations. So, build a training curriculum for your manual reviewers that covers every indicator discussed in this guide.
This will give your reviewers hands-on experience with the types of manipulation they’ll encounter daily.
How TruthScan Solves ID Image Review at Enterprise Scale
Manual document review can’t sustainably scale with your enterprise.
As submission volumes grow, your team can quickly become overwhelmed, leading to mounting pressure, slower verification times, and a higher risk of human error.
Hence, the gap between what human reviewers can reasonably examine and what fraudsters push through widens every quarter. The solution to bridge this gap is TruthScan.
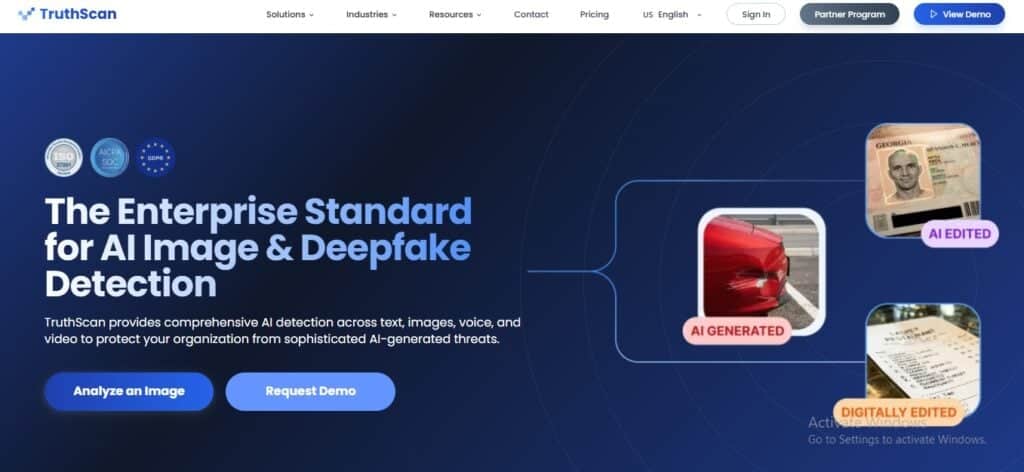
TruthScan is built for high-volume review queues where you need fast and clear evidence for enterprise verification demands.
Businesses using this platform enjoy an enterprise-grade real-time detector with sub-second processing and 99%+ detection accuracy.
| Your Operational Needs | TrutScans Offer | Resultado |
| Fake ID Detection | Quick analysis and API-based integration into existing workflow. | Lower review time per case, and fake ID approval is restricted. |
| Reliable Analysis | Heatmaps and pixel-level analysis outputs. | Clearer reviewer justification. |
| Actionable Identity Fraud Alerts | Probability scores and detailed analysis that will set off alert systems. | Cleaner escalation paths. |
| Audit readiness | Detection history dashboard and downloadable reports. | Easier internal reporting. |
Talk to TruthScan About Scaling ID Verification Safely
Fraudsters aren’t slowing down, and you can’t risk slowing down either.
Every manipulated ID that slips through your current system costs your business money, erodes your customers’ trust, and puts your compliance standing at risk.
Contact TruthScan today and get access to an account manager who’ll put you through enterprise-worthy plans as you scale your business and custom integrations that’ll seamlessly merge with your operations.
